How can the environment around computers be used to hack data? Computer scientists have now determined that it’s possible to send data or “steal” data by using heat transfer between computers – those typically used as servers in high profile institutions like banks and police. Their exercise in hacking heat points out vulnerabilities in today’s computer systems so security experts can build walls around them.
The researchers from Ben Gurion University developed what they are calling BitWhisper to breach into computer systems that use air gapped cooling. This breach lets the computers talk to one another through heat. Wow or what?
According to the researchers, “The scenario is prevalent in many organizations where there are two computers on a single desk, one connected to the internal network and the other one connected to the Internet. BitWhisper can be used to steal small chunks of data (e.g. passwords) and for command and control.
Stealing with a breath of warm air
“These properties enable the attacker to hack information from inside an air-gapped network, as well as transmit commands to it,” the BGU researchers explain. “Only eight signals per hour are sufficient to steal sensitive information such as passwords or secret keys. No additional hardware or software is required. Furthermore, the attacker can use BitWhisper to directly control malware actions inside the network and receive feedback.”
The research, conducted by Mordechai Guri, a Ph.D. student is part of an ongoing focus on air-gap security. Computers and networks are air-gapped when they need to be kept highly secure and isolated from unsecured networks, such as the public Internet or an unsecured local area network.
Typically, air-gapped computers are used in financial transactions, mission critical tasks or military applications.
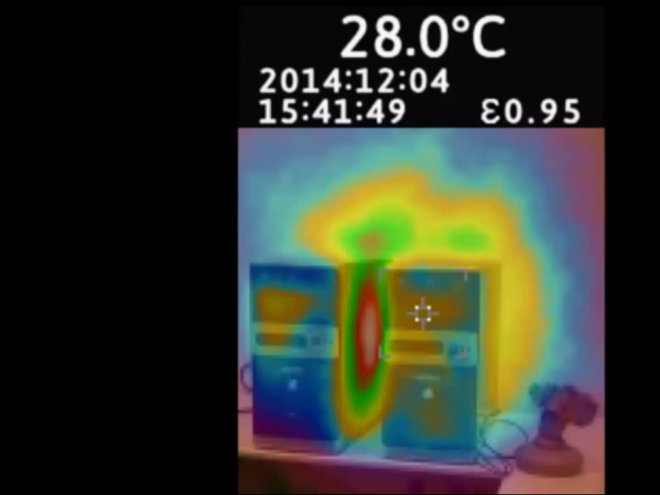
The new development of BitWhisper bridges the air-gap between the two computers, approximately 15 inches (40 cm) apart that are infected with malware by using their heat emissions and built-in thermal sensors to communicate.
It establishes a covert, bi-directional channel by emitting heat from one PC to the other in a controlled manner. By regulating the heat patterns, binary data is turned into thermal signals. In turn, the adjacent PC uses its built-in thermal sensors to measure the environmental changes.
These changes are then sampled, processed, and converted into data. Scary. Hackers stealing through heat. Let’s put minds like this on cracking bee colony collapse disorder and we’ll have started a revolution in bio hacking.



[…] Heat hackers breach computer systems by “breathing” data whispers Computer scientists have now determined that it's possible to send data or “steal” data by using heat transfer between computers – those typically used as servers in high profile institutions like banks and police. Their exercise in hacking heat points … Read more on Green Prophet […]